Virtual Machine Hardware Version does make a difference
For years, I have dismissed Virtual Machine Hardware version as unimportant. In fact, in this very blog, I may have advocated for leaving VM Hardware Version set at 8, to maintain full compatibility with both the vSphere C# Client and the vSphere Web Client.
Unfortunately, thanks to Spectre and Meltdown, things have changed. Updating your VM Hardware Version also updates the VM BIOS, and that’s an important part in the remediation of Speculative Execution Vulnerabilities, specifically: CVE-2017-5715 ‘Spectre Variant 2’.
Interestingly, this also highlighted another train of VMware: referring to the same thing by many names. In this case, we are talking about the Virtual Machine Hardware Version, but you will see the same thing called (by VMware) as:
- VM Compatibility
- VM HW
- VM Hardware
- VM Version
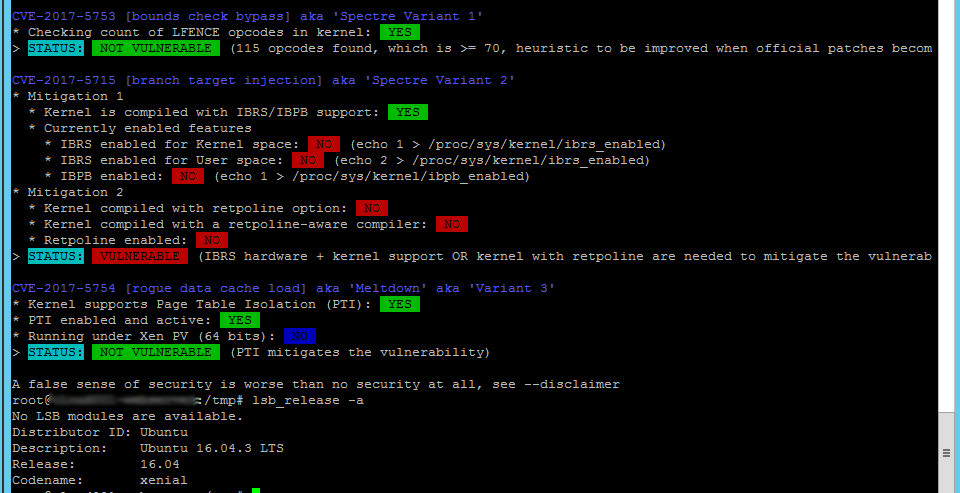
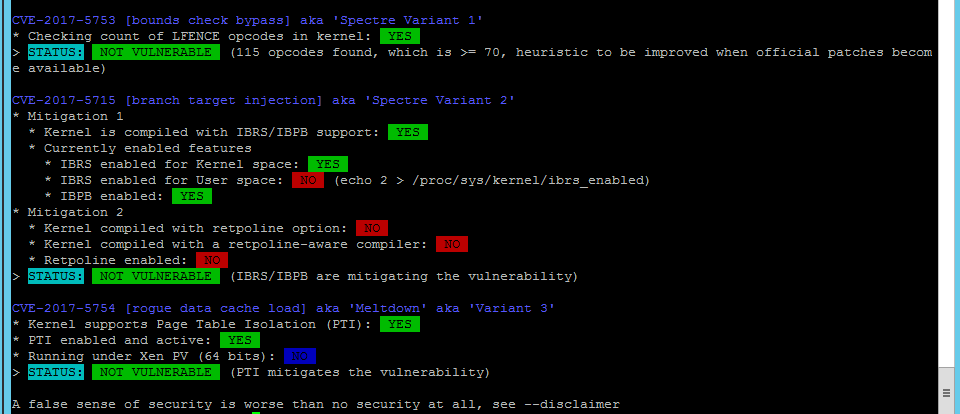
I used the Spectre Meltdown checker available on Github: https://github.com/speed47/spectre-meltdown-checker/blob/master/spectre-meltdown-checker.sh to obtain these results against a fully-updated (on 1/24/2018) Ubuntu 16.04.3 LTS server.
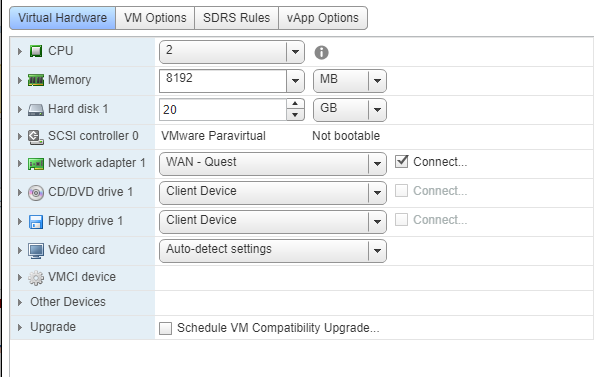
spectre-meltdown-checker.sh run against Ubuntu 16.04.3 LTS server with VM HW Version 8:
- Results show remaining vulnerability against CVE-2017-5715 ‘Spectre Variant 2’.
spectre-meltdown-checker.sh run against Ubuntu 16.04.3 LTS server with VM HW Version 11:
- Results show not vulnerable to CVE-2017-5715 ‘Spectre Variant 2’.
To upgrade your VM Hardware:
- In all cases, POWER OFF THE VM
- In the Windows C# Client:
- Right-click on the VM in the Inventory List and select: Upgrade Virtual Hardware
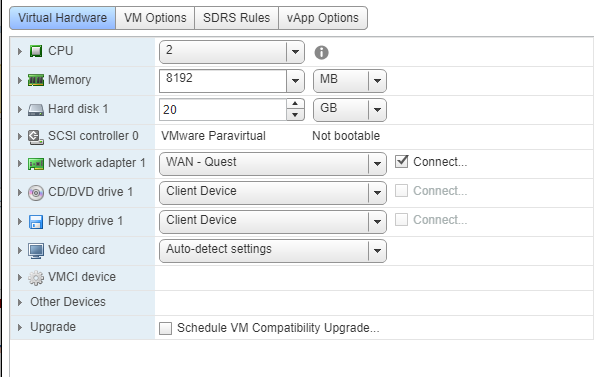
- In the vSphere Web Client:
- Right-click on the VM in the Inventory List
- Select: Edit Settings
- Check the box for “Schedule VM Compatibility Upgrade”
- Power-on the VM