Using WinSCP with the VMware vCenter Server Appliance
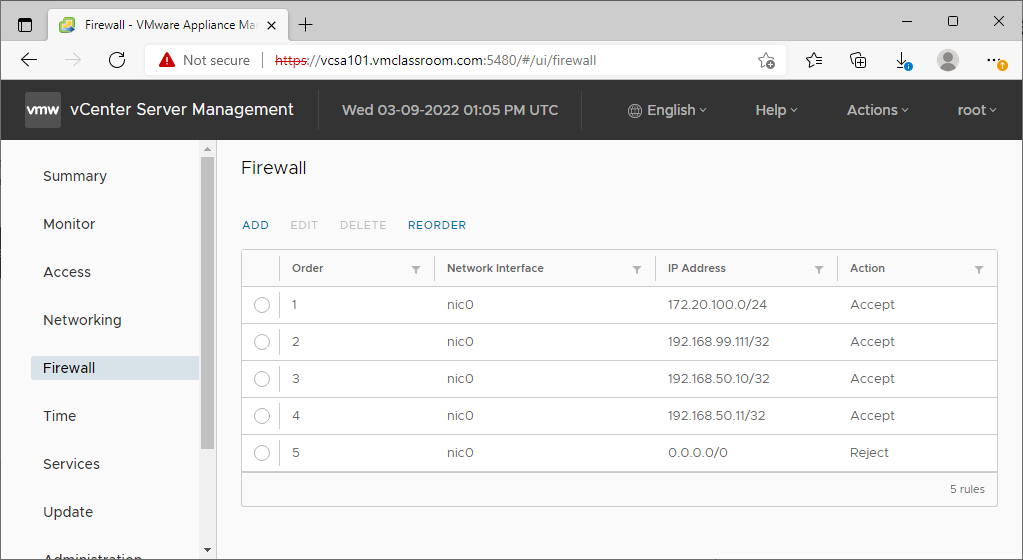
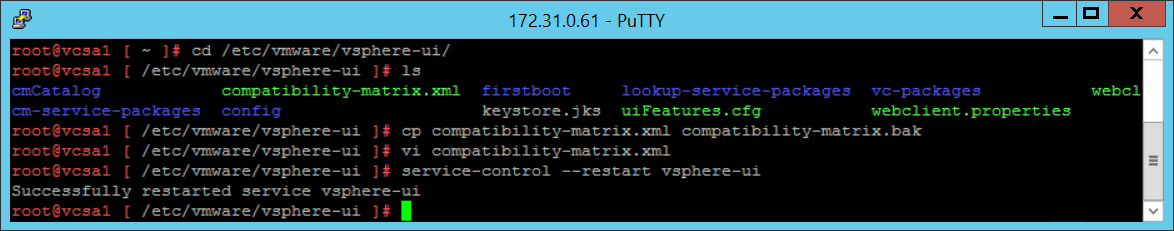
From time to time, you will find it necessary to transfer files to or from your VMware vCenter Server Appliance (VCSA) or ESXi Servers. If you are working from a Windows desktop or server, there’s no more convenient utility than WinSCP for copying files securely between Windows and Linux Systems. There are a few issues,
Read More »