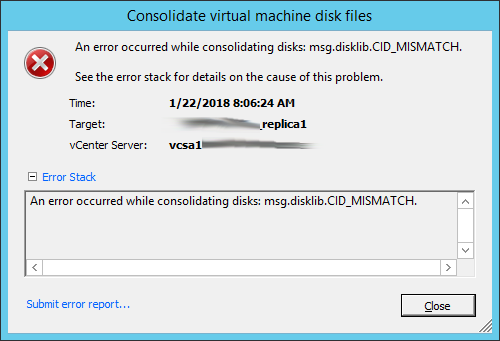
Invalid Snapshot Configuration
Invalid snapshot configurations happen. Mostly, they occur because of problems with storage arrays during snapshot creation/consolidation, but they can also occur if certain process become interrupted (like replication) mid-snapshot. The more heavily you rely on snapshots, the more likely it is you will come across a problem with snapshots. Specifically if you use a product
Read More »